CIA: Confidentiality, Integrity and Availability
CIA stands for Confidentiality, Integrity, and Availability and is considered a cornerstone in the field of cyber security.
CIA stands for Confidentiality, Integrity, and Availability and is considered a cornerstone in the field of cyber security. Every security strategy should include controls that minimize threats to these three elements. So, let’s analyze each one of these in detail.
Confidentiality
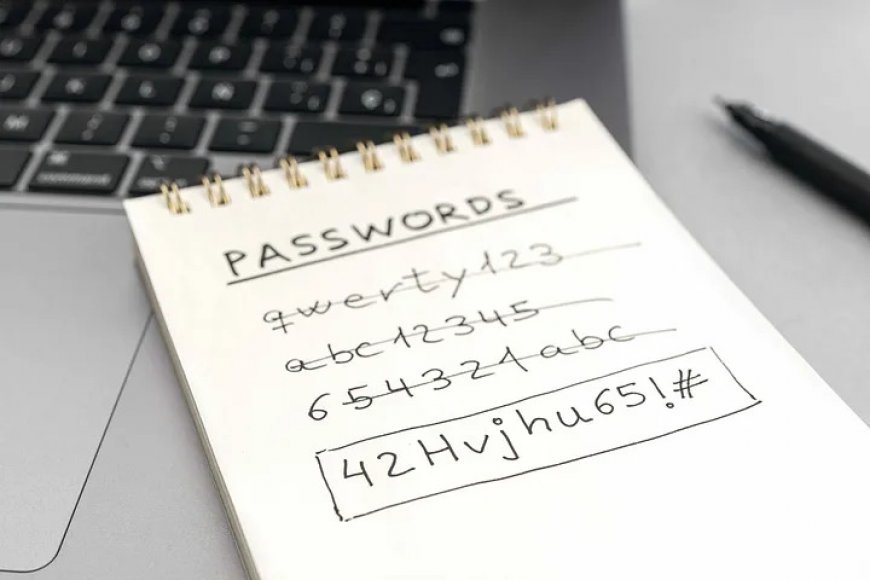
Let’s start with confidentiality. This refers to the need to ensure your data is confidential, meaning it can only be accessed by authorized users, at all times. This includes when data is stored, transmitted, and processed.

Some violations of confidentiality include:
● Breaking encryption: when someone manages to break your encryption, namely the code you used to protect your data
● Package sniffing: when your data is transmitted and someone captures your traffic
● Unintentional human errors: when someone accidentally exposes data to unauthorised users
The best way to enforce confidentiality is through encryption. Whenever you need to protect a file, you can use this tool to change the information on it to a language that is understandable only to those who have access to your encryption code.
If you’re a fan of fantasy, you can think of encryption as the Quenya language spoken by Elves in Tolkien’s novels, or the Klingon idiom on Star Trek. When you use this tool to protect your files, it is as if you were translating your file, letter by letter, from English to Klingon or Quenya. This makes it impossible for people to understand the information on your files unless they have access to a Quenya or Klingon dictionary, namely your encryption code.
Integrity
Integrity refers to the need for your data to be accurate, complete, and unmodified.

Violations of integrity occur when the receiver gets access to a file that has been modified. For instance, suppose you are taking part in a baking contest and are now working on a secret recipe. You need to leave the kitchen for a few minutes and decide to lock the room to make sure nobody will modify your dough, but when you come back, you realize someone has broken in. All your efforts have now been compromised. For instance, even though you may not see it, someone may have added a bit of baking powder to your dough, completely changing its final texture. This is what we call a violation of integrity and it often happens when transmitting data from one point to another. During this phase, someone may intercept your traffic, modify it, and then send it to the receiver as a corrupted version of the original. In other words, whenever the receiver gets access to a modified file, we say that its integrity has been violated.
People enforce integrity through so-called ‘hashes’. You can imagine these as summaries of your file. If someone happens to change the data in your file along the way, the hash will also change. Once the information arrives at its final destination, the receiver will be able to compare the hash he just received with the original one and see whether there are any differences. If yes, then something has been modified along the way.
Availability
Availability refers to the need to have data available as and when required. This means that your clients should have access to all the information they need whenever they need them.

Typical violations of availability include damage to your communication infrastructure. For instance, your clients may no longer be able to contact you at all or in a timely manner. A good example of this is someone who may send lots of traffic to your website with the sole purpose of slowing down your server. In this scenario, real clients interested in your services will be affected by the slowness of the server and may end up opting for a competitor. So, how can you prevent this from happening?
Availability is enforced through redundancy. In other words, you can install multiple communication links or database services so that if some of these stop working or slow down, the others will be able to take over.
If you liked this article, please checkout our course: Cyber Security: From Beginner to Expert
What's Your Reaction?